A top result on Google for people searching for Claude plugins sent users to a site that recently contained malicious code in an apparent attempt to steal their credentials.
The news shows how the explosion of interest in generative AI tools is giving hackers new ways to attack users.
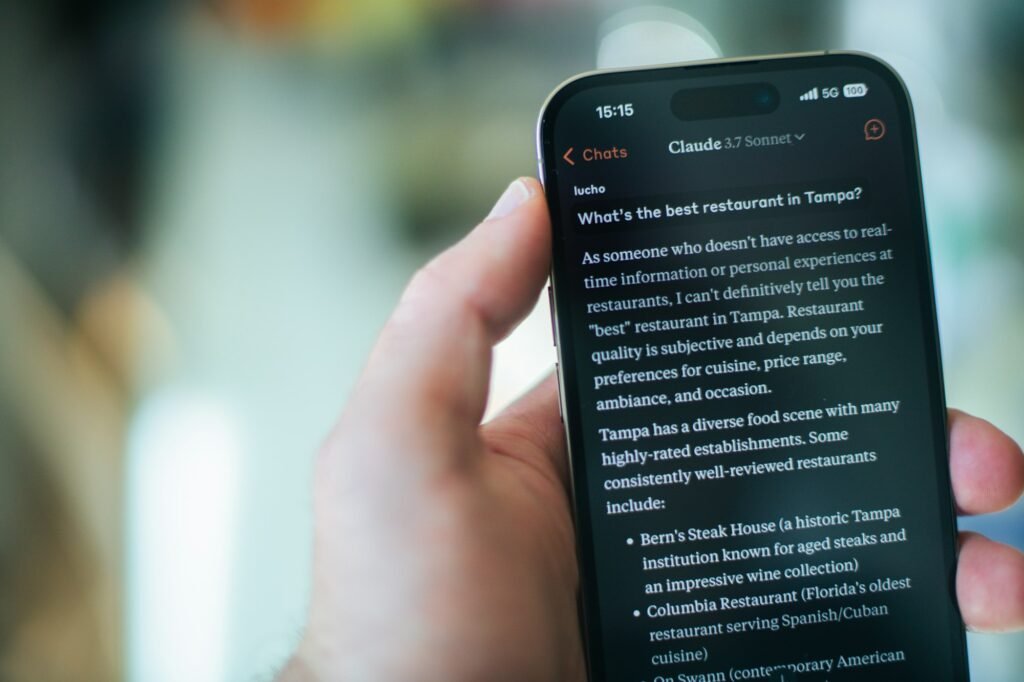
The malicious site was flagged to us by a 404 Media reader who was using Claude.
“I was googling to troubleshoot how to get my Claude Code CLI to authenticate its github plugin to my Github account and may have stumbled upon a malicious site hosted on Squarespace of all places,” the reader, Dan Foley, told me in an email.
Foley searched for “github plugin claude code” and the top result was a sponsored ad for a Squarespace site with the title “Install Claude Code – Claude Code Docs.”
When he clicked through, he saw a site that was pretending to be the official site for Anthropic’s Claude with identical design and branding.
The phony Anthropic help site had swapped some of the Claude Code installation instructions for others, Foley pointed out. That included a line users could paste into their terminal to allegedly install the software on a Mac. The command included an obfuscated URL, hiding what its real destination was. When Foley decoded it, he found it downloaded software from another site entirely.
ThreatFox, a platform for sharing known instances of malware, recently flagged that domain as sharing a “stealer”, a type of malware that steals users credentials. ThreatFox linked that domain to the stealer as recently as a few days ago.
Google’s ad center listed the advertiser behind the malicious sponsored search result as “Enhancv R&D,” which is based in Bulgaria, according to a screenshot of the advertiser profile Foley shared with 404 Media. The advertiser was also listed as being verified by Google, meaning they had to complete an identity verification process which requires legal documentation of their name and location.
Foley said he flagged the ad to Google, which removed the site from search results. The URL which pointed to the potential stealer is no longer online.
“We removed this ad and suspended the account for violating our policies,” a Google spokesperson told me in an email. Google said it has strict policies against ads that aim to phish information or distribute malware, and that it uses a combination of Gemini-powered tools and human review to enforce these policies at scale. Google claims the vast majority of these ads are caught before the ads ever run.
Malicious links included in paid Google ads that are pretending to be legitimate websites is not a problem that’s unique to AI. Hackers often try to get users to click malicious links by pretending to be whatever is popular on the internet at any given moment, be it a pirated movie or video game just before release or celebrity sex tapes. The fact that hackers are targeting Claude users reflects the growing popularity of AI tools and the hackers’ hope that users are not careful enough to check what they’re clicking when using them.
In January, we wrote about how hackers could similarly target users of the AI agent tool OpenClaw by boosting instructions for AI agents that contained a backdoor for hackers.
About the author
Emanuel Maiberg is interested in little known communities and processes that shape technology, troublemakers, and petty beefs. Email him at emanuel@404media.co
More from Emanuel Maiberg