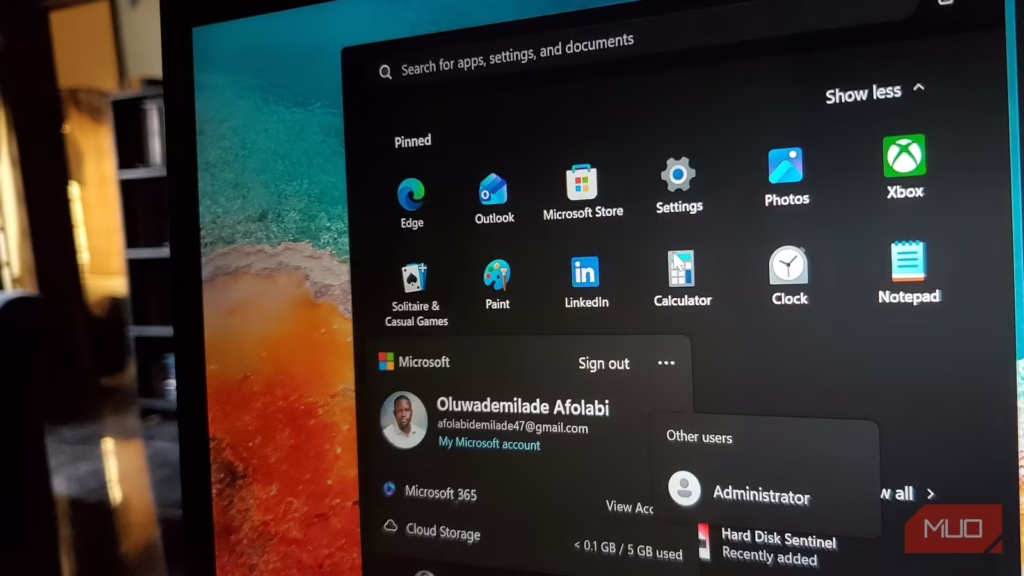
Most Windows users tend to assume that having an administrator account means they’ve reached the top of the food chain. You can install apps, poke around in system settings, and breeze past UAC prompts. While you likely understand the basic difference between a standard and an administrator account in Windows, that “Admin” status isn’t actually the final word on permissions.
Buried somewhere beneath your visible user accounts is one that makes your administrator account look like a polite suggestion. It doesn’t have UAC prompts to satisfy, confirmation dialogs to click through, and guardrails that Microsoft is particularly eager to highlight. It’s been around since the Windows XP days, ships with every Windows machine, and yet most people never run into it. Not because it’s hidden in some clever way, but because Windows keeps it turned off by default and doesn’t go out of its way to explain that it’s even there.
The account you call “Administrator” is still being supervised
Even the boss has a boss
When Windows Vista arrived, it introduced a feature called User Account Control (UAC) and promptly changed the relationship between admin accounts and absolute power. Before Vista, the built-in Administrator account was enabled by default, wide open, and basically handed every process on the computer a skeleton key. That went poorly, as you might imagine.
UAC introduced a behavior where even accounts with administrative privileges don’t automatically run every program with those privileges. It’s a mechanism that requires the user to take an additional step to run programs that access certain potentially dangerous system operations. The comparison people reach for is the super user account on Linux (often referred to as root), and it’s apt. Both provide unrestricted access to the underlying operating system and assume the person using them knows what they’re doing.
So your regular admin account, the one you likely set up when you first installed Windows, operates in a split mode. When an administrator needs to perform a task that requires a full administrator access token, Windows automatically prompts the user for approval. That’s the UAC dialog, and you’ve seen it thousands of times.
The built-in Administrator account has no such moment. It serves as the local system administrator with elevated rights by default, without needing “Run as administrator” or UAC approval for elevation. Every process you launch under it starts elevated.
In Windows XP and prior versions, this account was enabled by default. Microsoft disabled it starting with Windows Vista to reduce the attack surface of Windows PCs. The reasoning was that a password-less, all-powerful, always-on account is an excellent target if you’re trying to compromise a machine. Removing it from the equation by default was arguably one of the better security decisions Microsoft made in that era.
The default Administrator account can’t be deleted or locked out, but it can be renamed or disabled. It’s still there on every Windows installation, albeit just asleep. Which, under normal circumstances, is exactly where it should stay.
Waking it up is easy
Knowing when to put it back to sleep is the real skill
There are legitimate reasons to enable the built-in Administrator account. Troubleshooting deep permission issues, resetting a forgotten Windows administrator password to recover access to a locked-out system, making changes that even your regular admin account can’t seem to touch — these are the situations it was designed for. It was originally intended to facilitate system setup and disaster recovery.
To enable it, open the Command Prompt as an administrator and run:
net user Administrator /active:yes The account will appear on your login screen. To disable it again:
net user Administrator /active:no There’s also a PowerShell route if you prefer:
Enable-LocalUser -Name “Administrator” By default, the Administrator account is not password-protected, so the first thing you should do after enabling it is to set one. Run net user Administrator * in Command Prompt, follow the prompts, and create a strong password. An all-powerful account with a blank password sitting on your login screen is not a situation that ends well.
Because the account bypasses UAC and has unrestricted access, malware or unintended actions can cause system-wide damage if the account is left enabled. The same qualities that make the built-in Administrator useful for you make it incredibly useful for anything malicious running on your machine. Regular admin accounts limit the blast radius of a bad program. This one doesn’t. If you get infected with malware while signed into this account, it’s over — the Administrator account can’t stop it from spreading everywhere.
So what I’ll recommend is that you enable it, do what you need to do, then disable it immediately. Enable the built-in Administrator account only when necessary and disable it afterward to maintain system security.
The methods to enable it through graphical interfaces — such as Local Users and Groups (lusrmgr.msc -> Users -> right-click Administrator -> General tab -> deselect Account is disabled) or Local Security Policy (secpol.msc -> Local Policies -> Security Options -> Accounts: Administrator account status -> Local Security Setting -> Enabled) — are only available on thePro, Enterprise, and Education editions of Windows. If you’re on Windows Home, the Command Prompt and PowerShell routes work just fine.
Related
How to Open the Local Security Policy in Windows 11
Learn how to open the Local Security Policy in Windows.
Some doors are locked for your benefit
What’s interesting about all of this is what it says about the nature of administrative access on Windows. The everyday admin account — the one you use, the one most power users consider “full control” — is, in a technical sense, still managed, still leashed. The built-in Administrator is the version without the leash. Microsoft hid it for good reason, and after thinking about it for more than a minute, you’ll probably agree they made the right call.